BattleHack London
This past weekend it was London’s turn to take part in BattleHack 2015 and Pusher was invited by Braintree to be a BattleHack partner.
Introduction
The London Marathon wasn’t the only big competition that happened this past weekend. It was also London’s turn to take part in BattleHack 2015.
This year is the first year that we at Pusher have been invited by Braintree to be a BattleHack partner and the London event was the first of the finals that we’re going to be attending.
Jamie and I had been looking forward to it ever since we found out that we’d be going. We’ve both been to hackathons before and enjoyed them greatly so our expectations for BattleHack were set very high. Upon arrival at the venue we were met by those who had arrived early, itching to get their laptops out and start hacking.
Kicking Off
The gates opened at 10 and in streamed about 200 excited, technology-laden hackers all ready to compete to become the BattleHack champions of London and therefore be flown to the BattleHack World Finals later this year to represent London. The introductions were made, the contestants prepped, and everyone was given one of many meals before the starting gong was struck at 1pm on Saturday by the MC of the weekend, Cristiano Betta.

Anybody who had arrived without a team quickly found some teammates. Almost in an instant the main room was emptied as teams got to work in one of the three hacking rooms. Occasionally teams would send out someone who had a couple of questions or was struggling to get something working, or if they were in need of some refreshments, of which there was a more than plentiful supply. As partners of the event we weren’t competing but we got to help out with some teams and we were able to witness plenty of ideas transforming from something verbal or visual into usable apps and even some tangible hardware.

Screens littered around the venue provided teams with the time remaining to work on their hacks. As seems to happen with every hackathon that I’ve been involved with the time seemed to be ticking away as expected at the start; as the countdown got closer and closer to 0 it seemed to accelerate ever faster towards the final moments. Some teams were coding up until the very last second making sure that everything was in perfect shape before the demos began while other teams began to emerge from their respective rooms to witness the striking of the closing gong, performed by Charlotte Russell.


Hacking Over, Time to Present
After a short break for everyone to grab some fresh air as well as some food and drink it was time to get straight into the presentations. There were 45 teams that had signed up to present to the judging panel with each of them allowed 2 minutes to present with up to 1 minute of questions from the judges. Jamie and I got settled in at the front of the room to make sure that we had a good view of all of the hacks.
The overall quality of the hacks was really high, especially considering that the teams were only allowed 24 hours. Also we were thrilled to see plenty of teams had chosen to use Pusher as part of their hack. Here are a few of our favourite teams that used Pusher in their hack.
One of the first teams to present was called Team Goat. Their hack was centered around a mobile app that allowed a user to either type or speak an item or items that they wanted to buy and then be notified about the location of nearby shops that could sell them the item. The user’s request was sent to Team Goat’s server, processed, and then local shops would be asked if, and at what price, they could sell the requested product. The responses from the shops were then delivered back to the user in realtime with a proposed price and a location.

Last year’s winners were back again this year and participated under the team name MOAR Axes. I’m not sure I can fully do their hack justice using just words (and a photo) but I’ll try. It was an advertising platform that could be deployed to advertising screens along with a camera and beacons that could tell when passers-by were nearby and looking at the screen and therefore could then show them personalised adverts, only when they were engaged with the advert. The passer-by could then even purchase the goods or services shown in the advert by speaking to the screen.
Given that the screens all had cameras attached they could even be used to perform facial recognition on people and therefore spot people reported as missing. The hack was something to behold and it may well have been the case that the 2 minutes that they had to present wasn’t quite enough for them to fully explain everything that was going on.

Team Crowdless also combined beacons with Pusher in their hack. They created a mobile app that let users see if a given location was particularly crowded or not based on the number of devices that were near certain beacons. All of the locations that were setup to have crowd sizes tracked could be seen on a map that would update in realtime if more people arrived at the location or if people left a location.

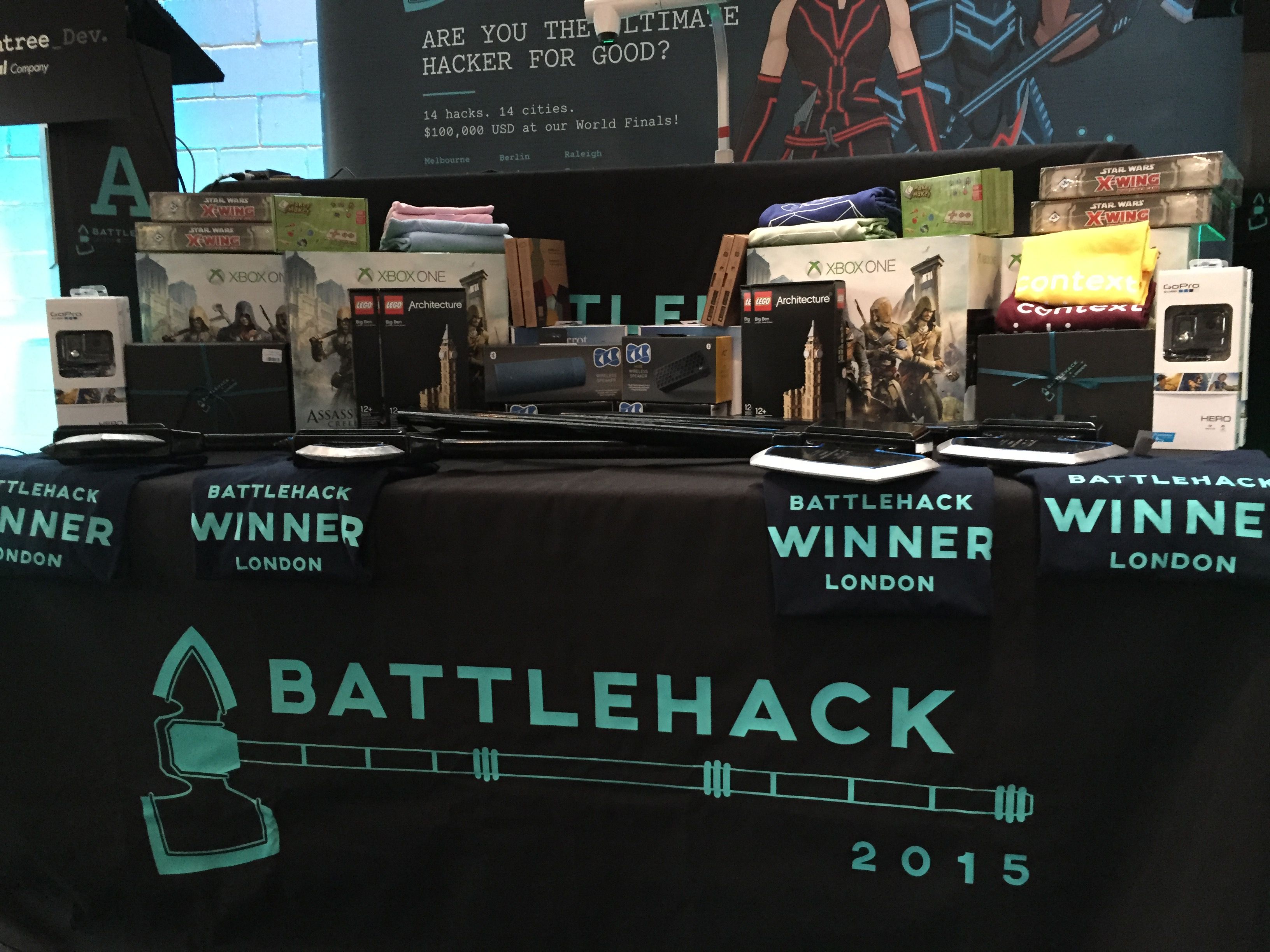
The Winners
The team that Jamie and I both agreed made the best usage of Pusher. They created a service that was designed with people who are at risk, for example, the elderly living alone. What it did was allow certain physical triggers to be setup, for example a kettle being used, or a television remote being pressed, and these events would then update a dashboard in realtime. If none of these pre-defined events occurred within a given timeframe then a welfare call would automatically be made to the at-risk person. If they didn’t respond then the person’s loved ones would be alerted.
It was a great idea that could, and almost certainly should, exist in the real-world. Not only was it an excellent idea but it was perfectly executed and even their live demo seemed to go down without a hitch.
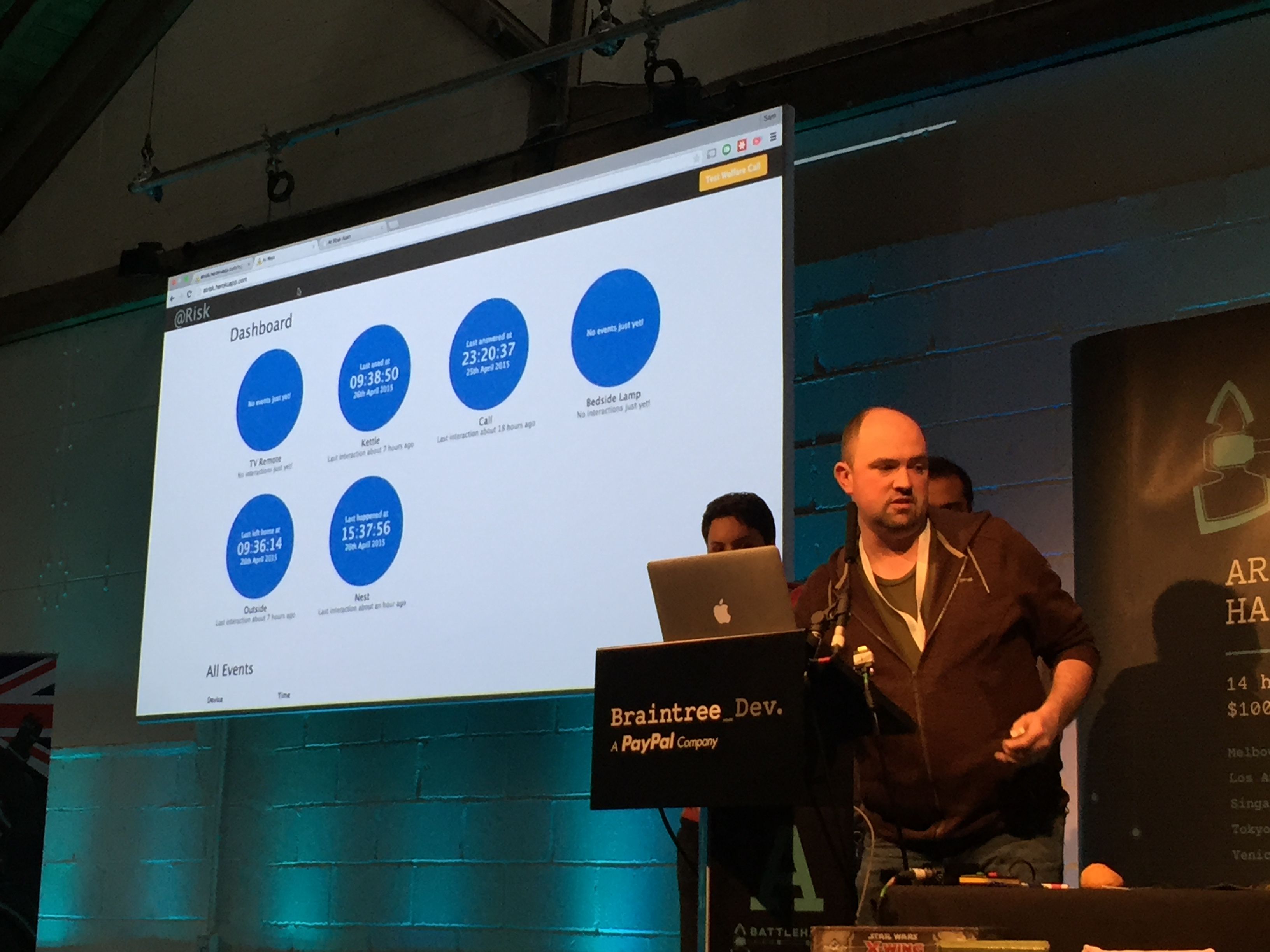
As it turned out, @Risk also won the Twilio and SendGrid prizes. Not only that, they were also crowned champions of BattleHack London and will therefore be representing London in November of this year at the World Finals!

A massive congratulations to all of the teams involved, but especially to @Risk.
BattleHack Athens can’t come soon enough!